
A security guard and a security program are not the same thing. Most organizations don’t know the difference until it’s too late.


A security guard and a security program are not the same thing. Most organizations don’t know the difference until it’s too late.

Hacked surveillance cameras helped plan the assassination of Iran’s Supreme Leader. The corporate security lesson has nothing to do with geopolitics.

Proven in Afghanistan, applied to boardrooms. Pattern of Life analysis is the intelligence methodology your corporate security program is missing.

How surveillance experience informs protective intelligence, threat vulnerability assessments, and recognizing risk before incidents occur.

Integrated security platforms combining ground sensors, automated cameras, and AI analytics deliver real-time threat detection, reduce false alarms, and strengthen organizational security effectiveness—when managed by trained professionals.

Nonprofits face rising cyber and workplace violence threats with limited budgets. Learn practical, cost-effective security strategies—from FEMA grants to NIST frameworks—that protect your mission, staff, donors, and clients.
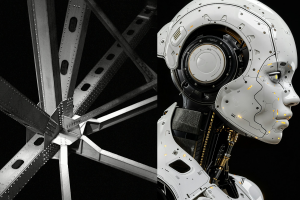
Explore the security implications of Pittsburgh’s industry transformation from steel to robotics and AI. Learn how tech firms must address IP theft, insider threats, and advanced manufacturing risks.

Security training alone doesn’t build strong defenses. Learn how organizational leadership, employee engagement, and meaningful measurement build a resilient security culture that reduces incidents and strengthens defense.

Automation, high employee turnover, and vendor reliance are increasing security risks in manufacturing and distribution. Discover how to protect assets, personnel, and critical operational continuity.

Security technology enables protection—but people and principles make it work. Learn why organizations focusing on principles-based security strategies outperform technology-first approaches.