| Jan 15, 2026
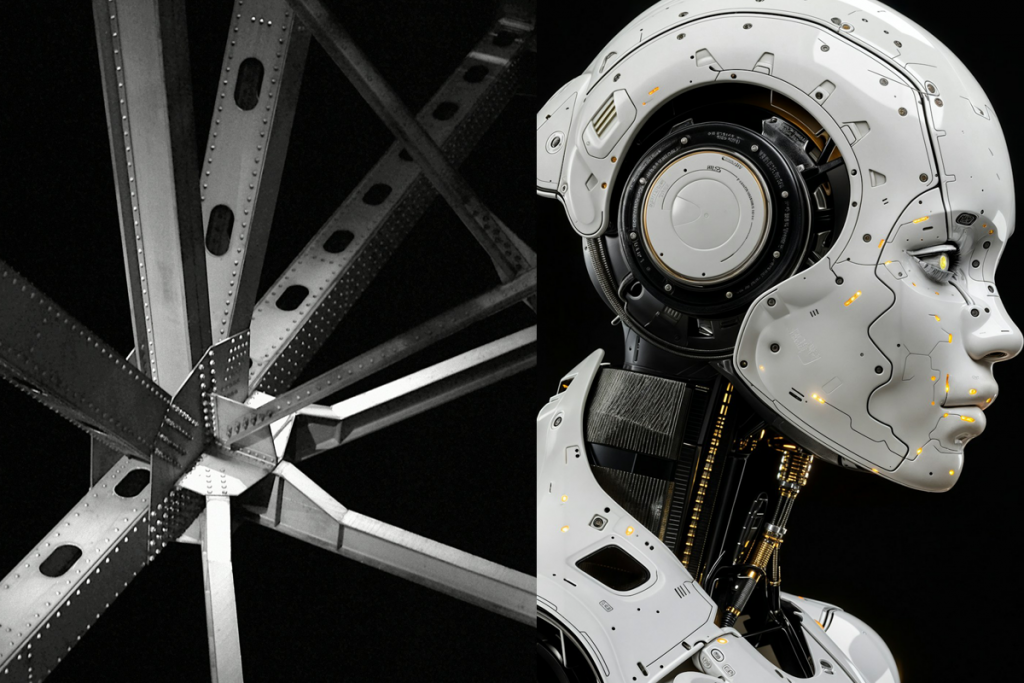
From Steel to Smart Tech: The Security Implications of Pittsburgh’s Industry Transformation
Pittsburgh’s transformation from steel capital to robotics and AI hub happened faster than anyone anticipated. Carnegie Mellon’s leadership in robotics, artificial intelligence, and advanced materials catalyzed economic development that attracted $3.12 billion in tech sector investment in 2023 alone. The region now houses 10,367 technology companies employing 283,779 people. Hardware and robotics represent 68% of regional investments.
This shift to smart tech created security implications that traditional industrial models never anticipated.
Intellectual Property Theft Risks to Pittsburgh Tech Industry
When your primary asset is steel, you secure the mill. When your primary asset is proprietary algorithms, robotics designs, and AI models, the threat surface expands in highly complex ways. Intelligence agency heads of “Five Eyes” countries – the U.S., Britain, Canada, Australia, and New Zealand – warned that China targets quantum technology, robotics, biotechnology, and AI through cyber intrusions, human intelligence operations, and corporate transactions.
Pittsburgh’s concentration of robotics startups, autonomous vehicle developers, and AI firms makes the region a target. Research facilities like Mill 19 and Neighbourhood 91 house collaborative environments where multiple companies share physical space. While this creates opportunities for innovation, it also increases the risk of insider threats and corporate espionage.
Different Physical Security Requirements for Smart Tech
Advanced manufacturing facilities face threats traditional factories never considered:
Access Control Beyond Basics
Manufacturing facilities require biometric authentication, role-based access systems, and segregated vaults for hardware under ITAR or EAR regulations. A single prototype theft can delay deployments by weeks and cost hundreds of thousands.
Surveillance With Intelligence
Modern industrial security incorporates AI-driven anomaly detection, not just cameras recording footage for post-incident review. Real-time monitoring, for example, identifies unauthorized photography in restricted areas as well as other suspicious activities.
Supply Chain Vulnerabilities
Researchers discovered backdoors in Chinese robotics products allowing hackers to control units remotely and conduct surveillance. As Pittsburgh manufacturers integrate more industrial robots – factories nationwide installed them at accelerated rates to compensate for workforce shortages – vendor security assessments become critical.
Data Exfiltration Monitoring
Industrial robots collect production schedules, product designs, and intellectual property data. Cloud and edge computing infrastructure creates data storage risks tied to IP theft. Organizations need monitoring systems tracking file sharing, USB activity, and cloud service usage; this is especially the case for departing employees.
Insider Threat Complexity in the Tech Sector
Pittsburgh’s tech workforce is mobile. People move between Carnegie Mellon research labs, startup accelerators like AlphaLab, and established companies. This mobility creates challenges: excessive code repository access, off-network development, unusual communication with competitors.
Warning signs include employees accessing information unrelated to assigned projects, increased file deletions before departure, and evidence of data wiping. Organizations need identity governance combining privileged access management with user behavior analytics.
What Tech Organizations Need to Enhance Security
The security frameworks that protected steel mills don’t protect robotics labs. Organizations in Pittsburgh’s evolving tech ecosystem require:
- Comprehensive access control with biometric authentication and audit trails.
- Surveillance systems integrating AI anomaly detection and real-time alerting.
- Insider threat programs monitoring code repositories and data exfiltration
- Vendor security assessments for robotics and IoT device suppliers
- Employee separation protocols analyzing forensic activity before departure
- Physical barriers designed for IP protection and not just theft deterrence
Pittsburgh’s industrial transformation brought economic growth and global recognition. It also brought adversaries interested in stealing what makes that growth possible. Organizations that recognize this reality and adapt security frameworks accordingly will protect what they’ve built. Those that don’t will fund their competitors’ R&D involuntarily.
For organizations evaluating where gaps exist in their current security posture, security consulting services such as threat and vulnerability assessments and audits provide a realistic baseline of protection capabilities, help identify priority investments, and serve as foundational documents to guide security strategy.
